Педро Луїс Мартін Оліварес
Колишній керівник відділу фінансової розвідки нині неіснуючого Управління розвідки та служб запобігання (DISIP), тепер Боліваріанської розвідувальної служби (SEBIN). Має офіційні звинувачення у суді Флориди з 2015 року за численні епізоди наркотрафіку. Звинувачується Сполученими Штатами у використанні своєї посади в уряді Венесуели для сприяння наркотрафіку через повітряний простір Венесуели.
| Ім'я | Педро Луїс Мартін Оліварес |
| Народився | 18 квітня 1967 |
| Місце народження | Каракас, Венесуела |
| Опис (DEA) | 1,65 м, ~113 кг, каштанове волосся, зелені очі |
| Винагорода | $10 000 000 (DEA) |
| Статус | Red Alert — Інтерпол |
| Псевдонім | Рамон Хосе Гаррідо Санчес (Фальшива особа) |
Передісторія
51-річний Мартін Оліварес з 2015 року висуває офіційні звинувачення в суді Флориди за кількома пунктами звинувачення в торгівлі наркотиками. Крім того, Сполучені Штати звинувачують його у використанні свого «посади» в уряді Венесуели для сприяння торгівлі наркотиками через повітряний простір Венесуели.
The U.S. Treasury Department added a former senior official of the Bolivarian Intelligence Service (SEBIN) and two of his alleged associates to its “blacklist” of drug traffickers, along with 20 “front” companies that were used to launder illicit money.
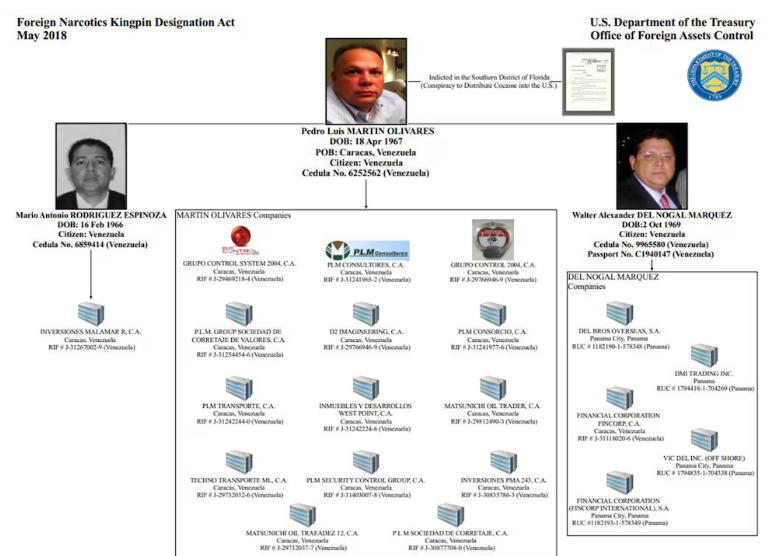
DEA розшукувало включення до списку та визначення Міністерства фінансів США
29 вересня 2020 року Державний департамент офіційно оголосив про винагороду в розмірі 10 мільйонів доларів через Програму винагород за наркотики (NRP). Мартін Оліварес значиться разом з іншими високопосадовцями венесуельського режиму.

Програма винагород Державного департаменту США за боротьбу з наркотиками — оголошення винагороди в розмірі 10 мільйонів доларів
Профіль суб'єкта та ідентифікаційні дані
Виявлення цифрового сліду
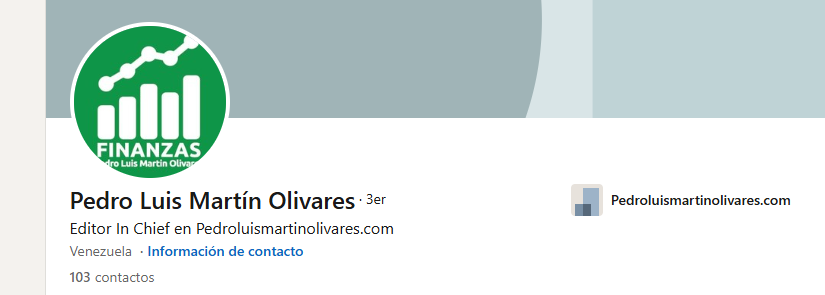
У своєму профілі LinkedIn він показує, як керує власним веб-сайтом.

Сторінка в Instagram з посиланням на тему
Аналіз інфраструктури веб-сайту
Сайт є інсталяцією CMS WordPress. Знайдено панель керування з базовим переліком.

CMS WordPress, ідентифікована на особистому веб-сайті суб’єкта
Легко знайшов cPanel — базовий перелік
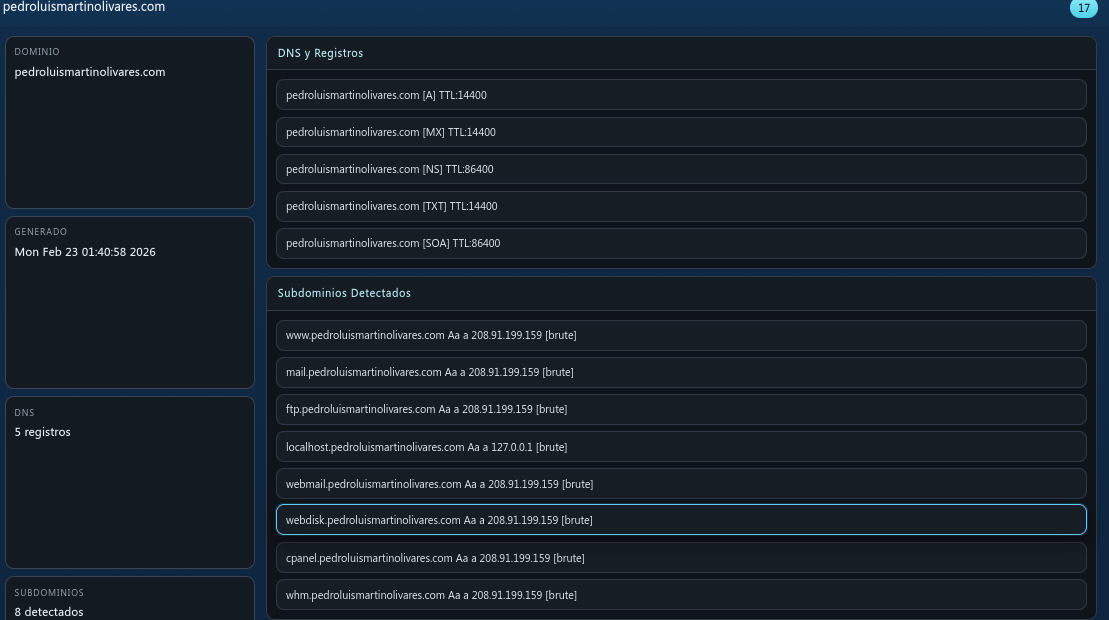
Розвідка піддоменів та DNS

Знайдено субдомени, інформацію про DNS та реєстратора
Відкриті порти
На сервері виявлено значну кількість відкритих портів
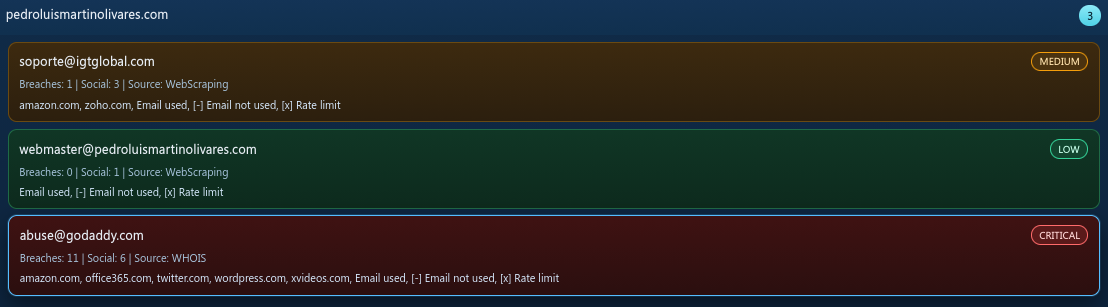
Електронні адреси
Електронні адреси, пов’язані з доменом
Виявлення акаунтів
Облікові записи, пов’язані з іменем користувача суб’єкта, були ідентифіковані на кількох платформах.
Виявлені вразливості
Під час аналізу інфраструктури було виявлено численні CVE та послуги.
| Суворість | CVE / ID | Сервіс | опис |
|---|---|---|---|
| ІНФО | інформація про mysql | Інтернет | [mysql-info] [javascript] [info] |
| ІНФО | snmpv3-detect | Інтернет | [snmpv3-detect] [javascript] [інформація] |
| ІНФО | imap-detect | Інтернет | [imap-detect] [tcp] [info] |
| ІНФО | mysql-detect | Інтернет | [mysql-detect] [tcp] [інформація] |
| ІНФО | pop3-detect | Інтернет | [pop3-detect] [tcp] [info] |
| ІНФО | mysql-native-password | Інтернет | [mysql-native-password] [tcp] [info] |
| ІНФО | tls-версія | Інтернет | [версія tls] [ssl] [інформація] |
| ІНФО | tls-версія | Інтернет | [версія tls] [ssl] [інформація] |
| ІНФО | spf-record-detect | Інтернет | [spf-record-detect] [dns] [info] |
| ІНФО | txt-відбиток | Інтернет | [txt-відбиток] [dns] [інформація] |
| ІНФО | caa-відбиток пальця | Інтернет | [caa-fingerprint] [dns] [info] |
| ІНФО | відбиток сервера імен | Інтернет | [nameserver-fingerprint] [dns] [info] |
| ІНФО | mx-відбиток | Інтернет | [mx-відбиток] [dns] [інформація] |
| ІНФО | ssl-емітент | Інтернет | [ssl-issuer] [ssl] [info] |
| ІНФО | ssl-dns-імена | Інтернет | [ssl-dns-names] [ssl] [info] |
| ІНФО | wildcard-tls | Інтернет | [wildcard-tls] [ssl] [інформація] |
Спроба доступу до бази даних
Під час спроби входу в базу даних MySQL сервера з’єднання було заборонено системою запобігання вторгненням хоста.
Підключення заборонено сервером IPS під час спроби доступу до бази даних MySQL
У виробництві
Це розслідування триває. Додаткові висновки, глибший аналіз інфраструктури та підтверджуючі дані розвідки будуть опубліковані в ході розслідування.
Примітка слідчого
This report is based entirely on open-source intelligence (OSINT). No classified information was accessed. No confidential sources were used. Everything documented here is publicly available — if you know where to look.
